Fact check: Does the StopCovid app contain a tracking device?
On Tuesday, June 2, 2020, the StopCovid app was released on the Apple App Store and the Google Play Store (Google). Developed by several companies, including Dassault Systèmes, Capgemini, and ATHOS, and led by the French National Institute for Research in Computer Science and Control (INRIA), to facilitate the contact tracing of COVID-19 patients and their potential contacts, StopCovid was approved bythe National Assembly and the Senate on May 28, 2020.
Florence Rodhain, University of Montpellier

From its conception to its approval, however, the app has never been universally accepted, with critics expressing particular concerns about the security of users’ personal data.
On social media, the organization La Quadrature du Net, which promotes and defends fundamental freedoms in the digital realm, has even expressed concern about the presence of a “spy”: the reCAPTCHA system. Designed by and linked to Google, this verification system reportedly sends data about our internet browsing directly to the U.S. company.
Did the developers of StopCovid include a "tracking feature" in the app? The answer is "yes," and that deserves an explanation.
A request for input and concerns
On May 15, 2020, Olivier Véran, Minister of Solidarity and Health, referred a draft decree concerning the “StopCovid” mobile app to the National Commission on Informatics and Liberties (CNIL) for its opinion.
Ten days later, the CNIL, which had to work under tight deadlines, issued an opinion on this application. In note 77 of this opinion, the CNIL expressed concern that the ministry plans to use a “Captcha” (an automated system designed to verify that the application is being used by a human user), and that this service would be provided by a third party. The commission is therefore alarmed by the fact that “the use of this service is likely to result in the collection of personal data not provided for in the decree, data transfers outside the European Union, as well as read/write operations that would require the user’s consent.”
CAPTCHAs are systems designed to combat spam bots. In the case of the StopCovid app, the goal is to ensure that a real person is using it. There are various types of CAPTCHAs developed by different companies. The most common CAPTCHAs consist of codes (numbers and letters) that are difficult to decipher, which the user must type in.
Lines of code
On May 27, on Twitter, La Quadrature du Net revealed that the StopCovid app includes a Google tracking tool called reCAPTCHA. In its tweet, the organization linked to lines of code on the Inria website where the use of Google’s services can indeed be clearly seen.
La Quadrature du Net is also concerned that, if this tracking feature remains in the app, the government would have failed to honor its commitments, even though Cédric O, the Secretary of State for Digital Affairs, had emphasized the importance of the principle of “digital sovereignty” just a few weeks earlier before the Senate.
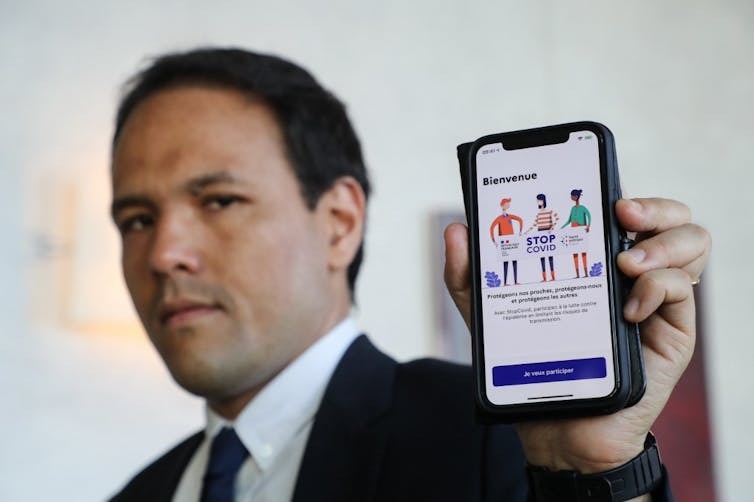
Ludovic Marin/AFP
In fact, the entire process was designed to remain within European borders without relying on Google or Apple’s services. That is why the application was led by Inria.
The answer is in the source code
So, what’s the deal? Does the StopCovid app still contain that tracking feature? Or has the government heeded the CNIL’s concerns and consequently asked Inria to use a Captcha technology other than Google’s?
To answer this question, simply visit the Inria website and read the source code, where you’ll still find a reference to Google’s reCAPTCHA.
So, yes, at present, the StopCovid app does indeed contain a “tracking mechanism,” as La Quadrature du Net asserts, since it can record the IP (Internet Protocol) addresses of phones on which the app is installed, which appears to contradict the principles of consent and privacy-by-design (principles of consent that must be taken into account from the very design of the app) of the European General Data Protection Regulation (GDPR) upheld by the CNIL. This is indeed personal data; the app is therefore not entirely anonymous, as had been announced from the start.
When asked to explain the matter, Cédric O said in an interview that Google’s reCAPTCHA—the “only element that wasn’t developed by us”—was chosen because “on the mobile version, there were no other CAPTCHAs available that could handle the strain of several million interactions.”
It is worth noting that Orange is reportedly working on a solution to eliminate the need for Google’s services and reCAPTCHA; this solution could be available soon. If Orange succeeds, there will no longer be any “tracking” to worry about in the StopCovid app. It remains to be seen when Orange will finalize this work and whether, by that time, it will still be relevant to use the app…
One snitch can hide another
Ultimately, one could argue that this “spyware” is not intentional but rather the result of an unintended consequence stemming from the lack of an alternative solution—though this remains to be proven. However, an article in *Le Monde* describes a completely different, far more insidious intrusion, and it is hard to believe that this one is not intentional.
In this article, Gaëtan Leurent, a French cryptography researcher at Inria, explains that he discovered, on the StopCovid app’s development platform, that all contacts with people encountered—regardless of the duration of those contacts—over the past 14 days are sent to the central server hosting the app’s data. “StopCovid therefore sends a large amount of data to the server that is irrelevant for tracking the spread of the virus, but poses a real threat to privacy,” the researcher explains in Le Monde.
The explanations provided by the Secretary of State for Digital Affairs appear questionable. When contacted by Mediapart, the Secretary of State for Digital Affairs did not dispute these revelations, but sought to justify them. It explains that every 15 minutes, a new identifier is assigned to each device. Thus, a contact lasting only five minutes could follow a 12-minute contact: two contacts that only the server is capable of linking to understand that they are, in reality, a single contact lasting 17 minutes—and therefore risky.
These explanations do not convince researcher Gaëtan Leurent, who believes “there are fairly simple ways to mitigate the problem: the phone could filter the data to retain short contact durations only when they occur immediately before or after a change in the identifier.”
What’s most concerning is that the Secretary of State’s explanations came after the app had already been rolled out. If all of this turns out to be true, we should be more worried about this second spyware than about Captcha!
This fact-check was conducted in partnership with the Journalism and Science program at the ESJ in Lille.![]()
Florence Rodhain, Associate Professor (HDR) in Information Systems, University of Montpellier
This article is republished from The Conversation under a Creative Commons license. Readthe original article.